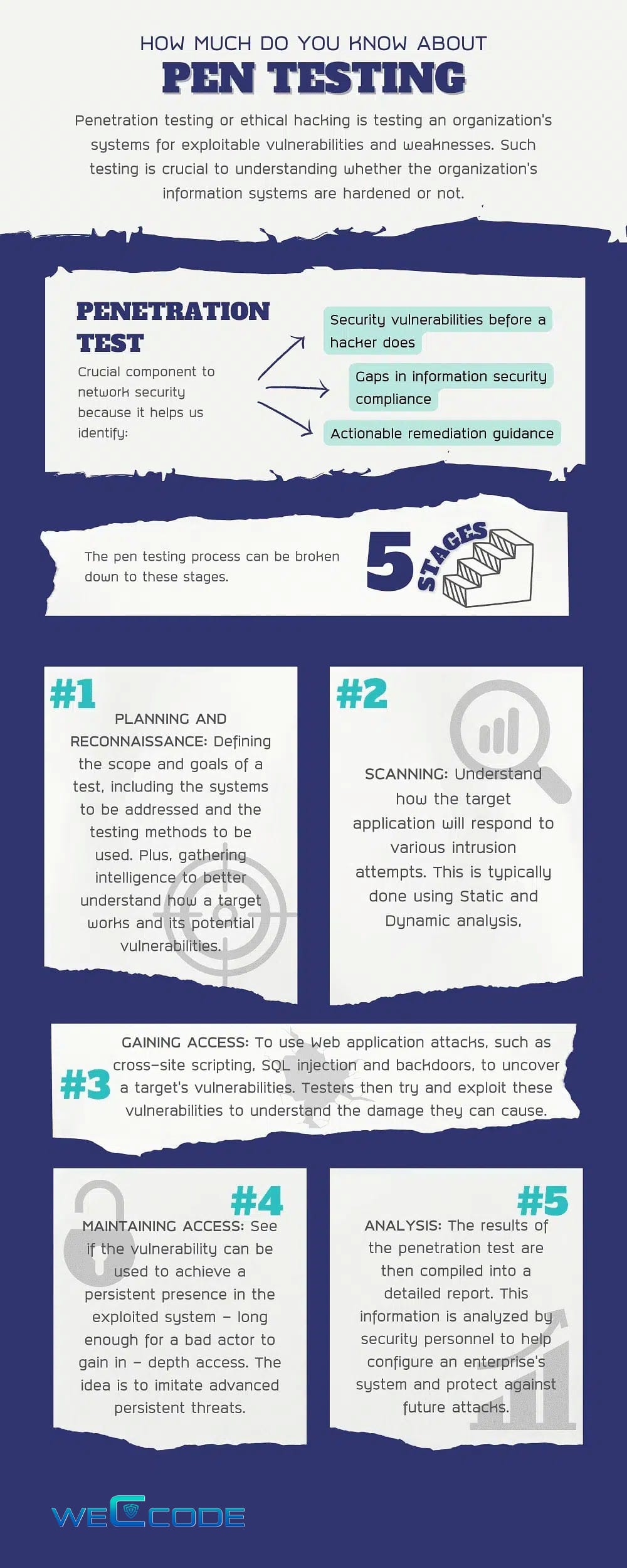
Pen Testing

Penetration testing or ethical hacking is testing an organization’s systems for exploitable vulnerabilities and weaknesses. Such testing is crucial to understanding whether the organization’s information systems are hardened or not. A hardened information system must be able to withstand malicious attacks. Penetration testing challenges a network’s security. Given the value of a business’s network, it is imperative that businesses consult with experts before pen testing. A penetration test starts with the security professional enumerating the target network to find vulnerable systems and/or accounts. This means scanning each system on the network for open ports that have services running on them. It is extremely rare that an entire network has every service configured correctly, properly password-protected, and fully patched. Once the penetration tester has a good understanding of the network and the vulnerabilities that are present, he/she will use a penetration testing tool to exploit a vulnerability in order to gain unwelcome access. A penetration test is a crucial component to network security. Through these tests a business can identify:
- Security vulnerabilities before a hacker does
- Gaps in information security compliance
- The response time of their information security team, i.e. how long it takes the team to realize that there is a breach and mitigate the impact
- The potential real-world effect of a data breach or cybersecurity attack
- Actionable remediation guidance
The pen testing process can be broken down into five stages.
1. Planning and reconnaissance
- Defining the scope and goals of a test, including the systems to be addressed and the testing methods to be used.
- Gathering intelligence (e.g., network and domain names, mail server) to better understand how a target works and its potential vulnerabilities.
2. Scanning
- Static analysis – Inspecting an application’s code to estimate the way it behaves while running. These tools can scan the entirety of the code in a single pass.
- Dynamic analysis – Inspecting an application’s code in a running state. This is a more practical way of scanning, as it provides a real-time view into an application’s performance.
3. Gaining Access
4. Maintaining access
5. Analysis
- Specific vulnerabilities that were exploited
- Sensitive data that was accessed
- The amount of time the pen tester was able to remain in the system undetected
Pen testing by
Real-world experts using the best
tools today!